What is Cybercrime?
Cyber-crime is criminal activity carried out using the internet, computers, or mobile devices. It is a major threat to businesses and individuals, and involves fraudsters or hackers unlawfully accessing confidential data or program files for the purpose of fraudulently obtaining money through coercion. According to the FBI’s Internet Crime Complaint Center (IC3), cyber-criminals were responsible for $2.7 billion in financial losses in 2018. This is a 238% in losses reported to the Center since 2014 (an average increase of 60% per year). This staggering upsurge clearly indicates that the scams used by cyber-criminals to target businesses are becoming increasingly more sophisticated. In spite of the geographic location of a fraudster, cyber-crime has no borders. Attacks can come from anywhere in the world, which makes transnational evidence gathering, as well as the ultimate identification and prosecution of the perpetrator(s), extremely difficult.
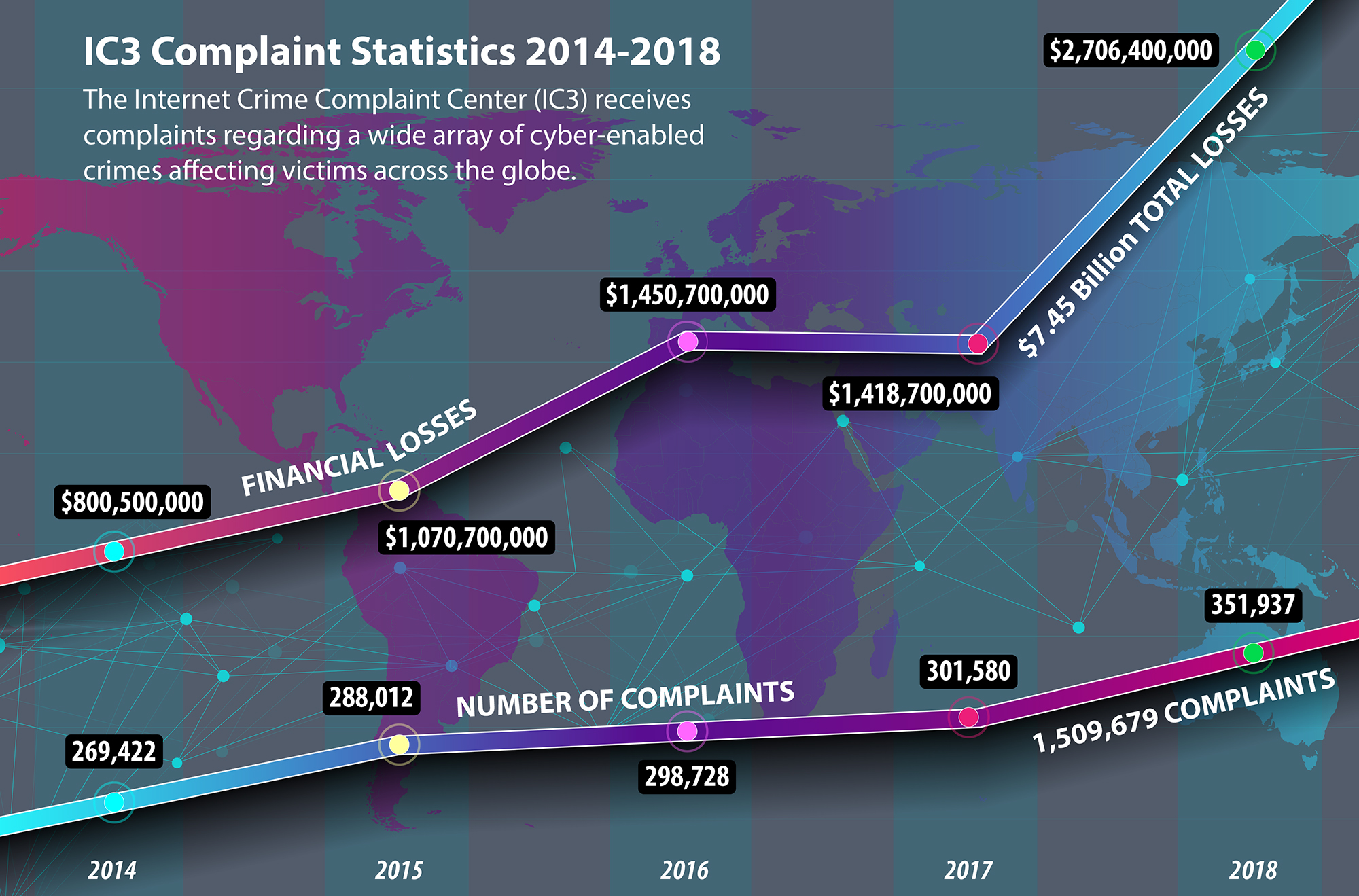 Source: FBI
Source: FBI
The Association of Certified Fraud Examiners identifies the 10 most common scams as:
1. Ransomware
2. Tech Support Fraud
3. Charge-back Fraud
4. Business Email Compromise
5. Over payment Scams
6. Vanity Award Scams
7. Phony Invoice Schemes
8. Advance-Fee Schemes
9. Business Identity Theft
10. Search Engine Optimization Scams
While many techniques will overlap, each of these 10 styles of cyber-crimes are unique and employ a specific MO. Over the coming months, I will use this platform to dive deeper into each of these 10 types of cyber-crime, and beginning with the top of the list…
This term may already be familiar after the notorious WannaCry attack of 2017 made international news. Reportedly the largest global ransomware attack in human history, WannaCry affected approximately 200,000 computers in 150 countries. The malware (malicious software) targeted unpatched Windows systems, encrypting files and making them inaccessible to the user. To regain access to their files, the hackers demanded victims pay a “ransom” of $300-$600 in Bitcoin. Countless individuals and organizations were affected, including the United Kingdom’s National Health Service and Sony Pictures. Experts estimated total damages between $500 million and $4 billion, and most intelligence sources trace the origins of the attack back to North Korea.
What happens in a Ransomware attack?
A successful attack usually looks something like this:
1. A computer or network becomes infected without your knowledge, usually through covert methods such as phishing emails.
2. Once the malware has access to the computer system, it infects the network or computer and encrypts or locks access to files and data.
3. The malware then corrupts and removes backup data, removing the data’s safety net. To avoid permanently losing precious files, the victim may feel forced to pay a ransom.
4. The victim is presented with a ransom demand, displayed on their computer screen, which threatens to permanently delete files and folders unless the ransom is paid.
5. While some paid and regained control, some other victims paid and still did not receive access to their files, or they were infected again.
How to Protect Your Business from a Ransomware Attack
- Train employees annually on cyber-security
- Have clear cyber-security policies and procedures, and consistently send out cyber-security reminders and notifications of reported cyber-attacks
- Always keep firewalls turned on when using for an Internet connection
- Install or regularly update anti-virus and anti-spyware software on all computers throughout the organization
- Back-up all business data (operations; HR; finance; legal) in a segregated location to prevent ransomware from deleting backups on the same network or device
- Enforce strict security protocols to access computers and network systems, and change passwords frequently
- Have adequate physical security controls for gaining access to hardware and data
- Ensure the business WiFi network is secure and hidden
- Limit employee access to data (access should correspond to an employee’s security level, job description, and duties)
- Limit authority to install software
 About the Author: Bernard's role as EVP, Chief Compliance Officer for AscendantFX, and previously as a Commander in the Royal Canadian Mounted Police (RCMP) investigating organized crime, allows him to be uniquely qualified to give insight into the dangers which these many different frauds, scams, and hacks present to businesses and individuals.
About the Author: Bernard's role as EVP, Chief Compliance Officer for AscendantFX, and previously as a Commander in the Royal Canadian Mounted Police (RCMP) investigating organized crime, allows him to be uniquely qualified to give insight into the dangers which these many different frauds, scams, and hacks present to businesses and individuals.